Configuring SAML SSO for ManageEngine Access Manager Plus
The following steps will help you enable single sign-on (SSO) to Access Manager Plus from ADSelfService Plus.
Prerequisites
- Ensure that the ADSelfService Plus server can be accessed through an HTTPS connection (the Access URL must be configured as HTTPS).
- Log in to ADSelfService Plus as an administrator.
- Navigate to Configuration > Self-Service > Password Sync/Single Sign On > Add Application, and select Access Manager Plus from the applications displayed.
Note: You can also find Access Manager Plus from the search bar located in the left pane or the alphabet-wise navigation option in the right pane.
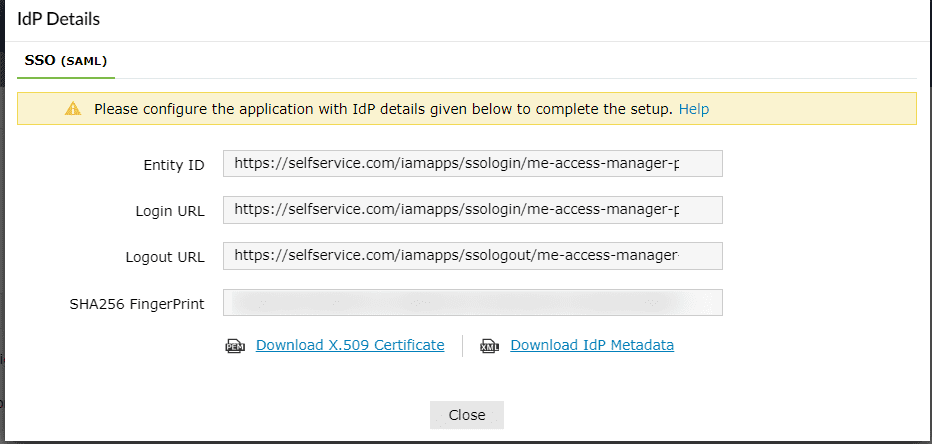
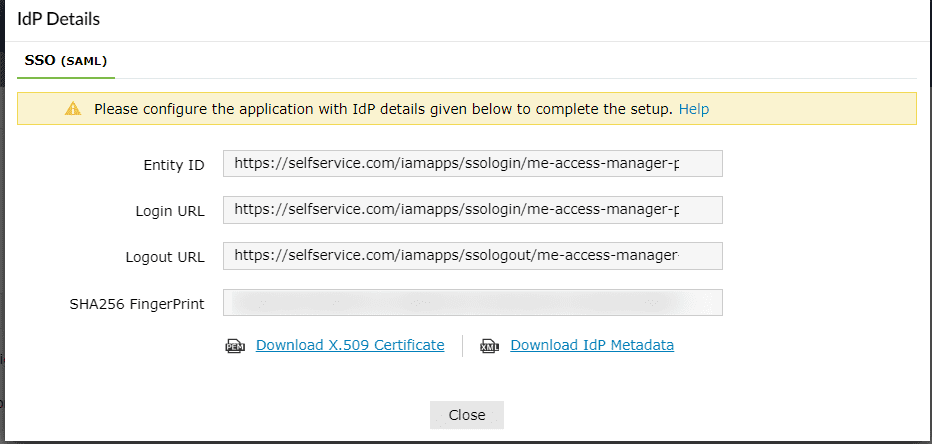
- On the Access Manager Plus configuration page, click IdP Details in the top-right corner of the screen. A pop-up will appear.
- You can configure the identity provider details in Access Manager Plus by either uploading the metadata file or entering the details manually.
- Uploading the metadata file: Download the metadata file to be uploaded during the configuration of Access Manager Plus by clicking the Download IdP Metadata link.
- For manual configuration: Copy the Entity ID, Login URL, and Logout URL, which will be used during the configuration of Access Manager Plus. Download the SSO certificate by clicking the Download X.509-Certificate link.
Access Manager Plus (service provider) configuration steps
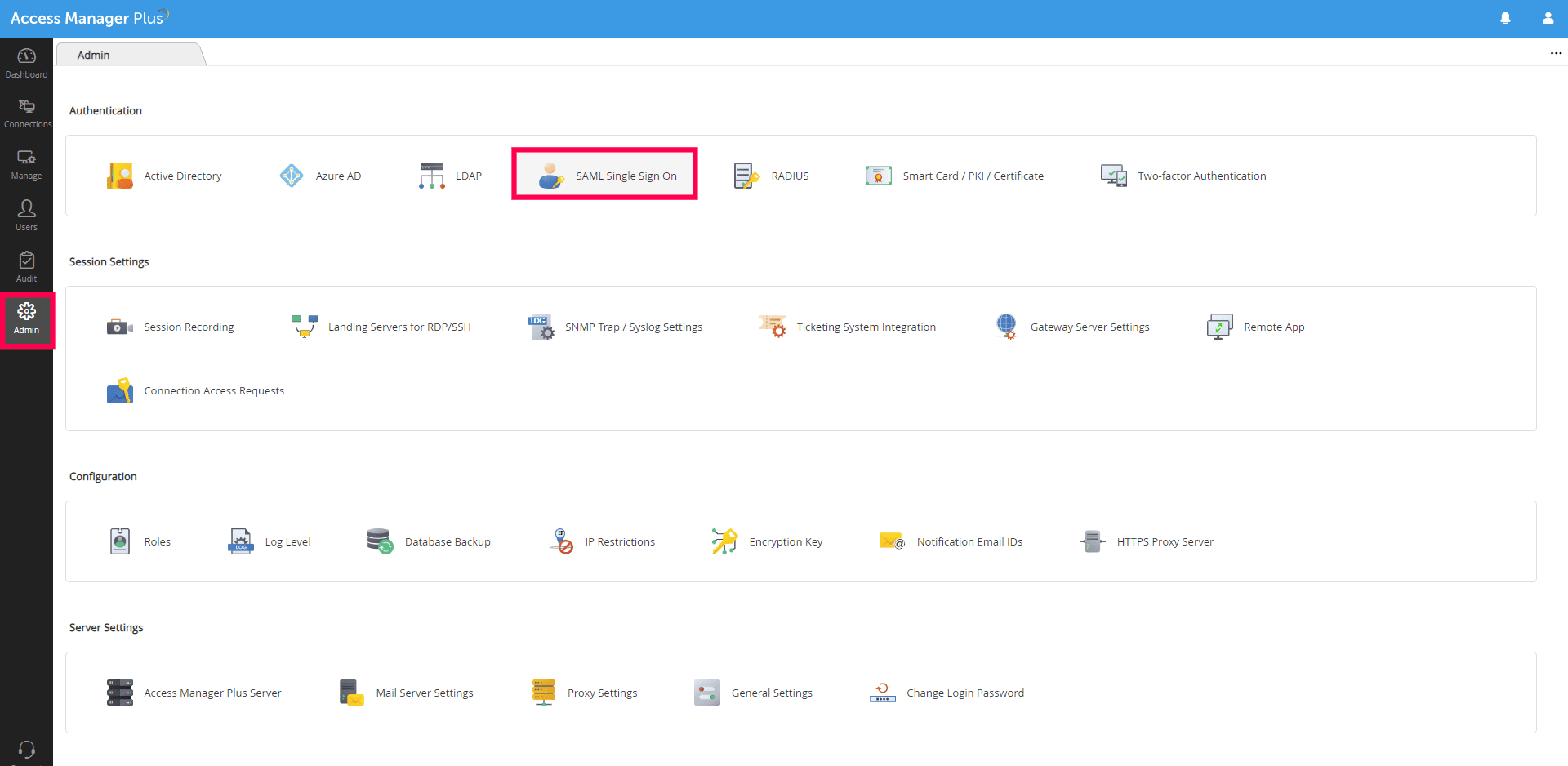
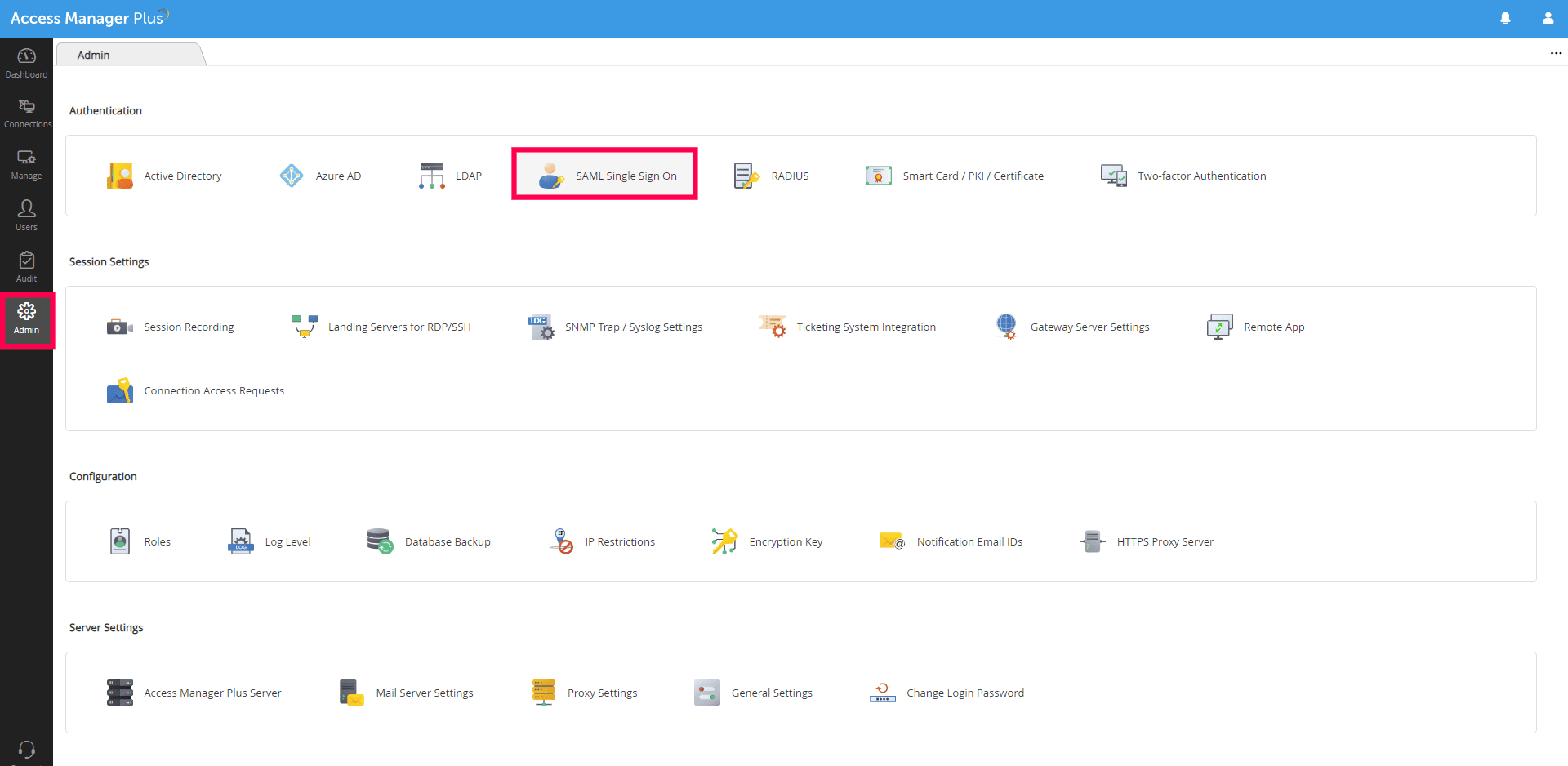
- Log in to Access Manager Plus with administrator credentials.
- Navigate to Admin > SAML Single Sign-On.
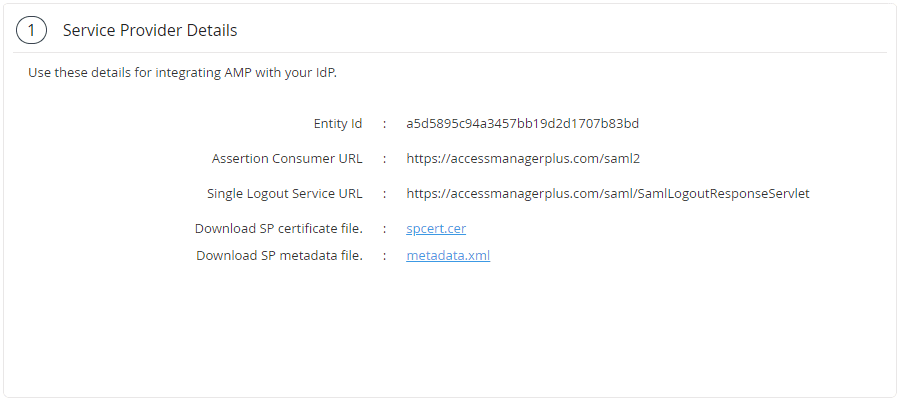
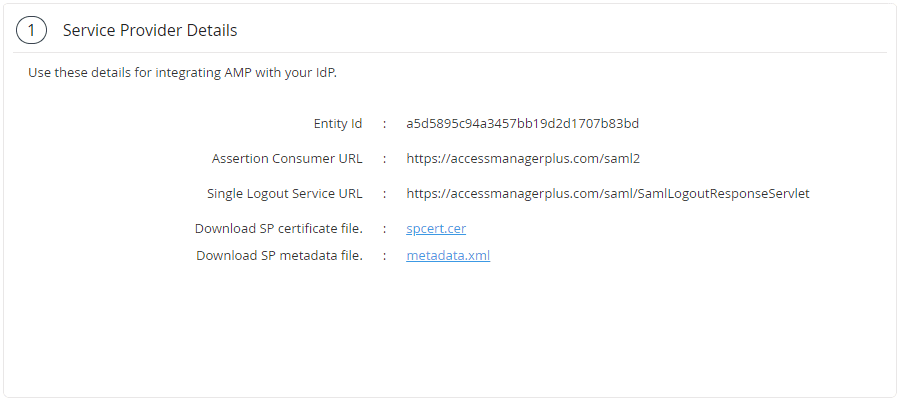
- Copy the values of the Entity Id and the Assertion Consumer URL from the Service Provider Details section; these will be used later.
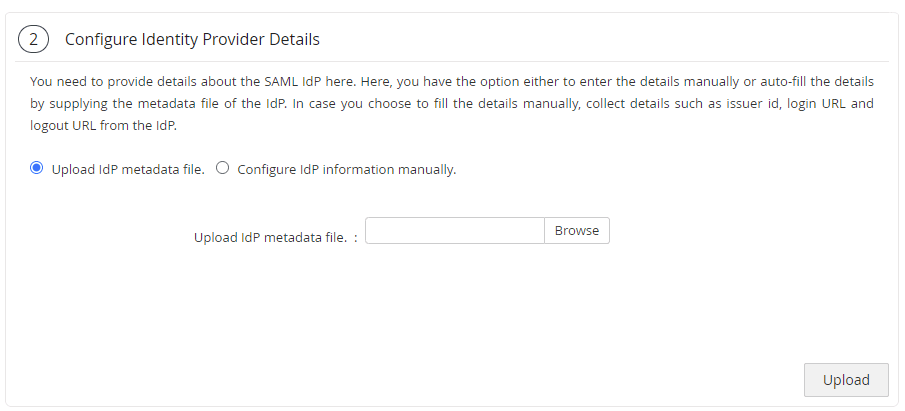
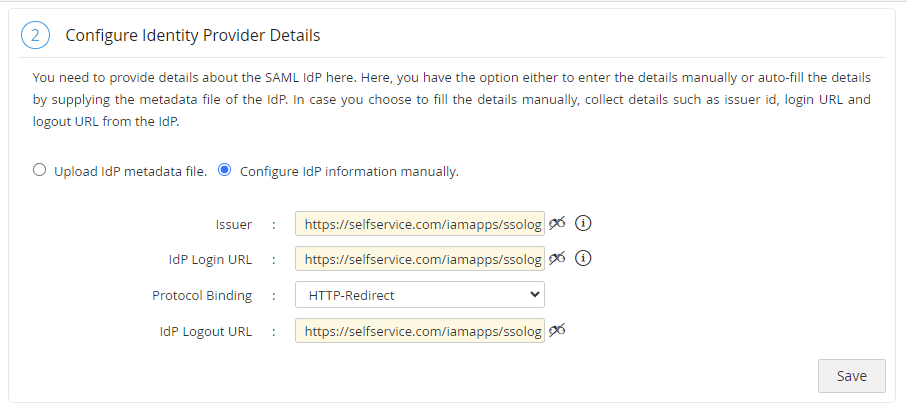
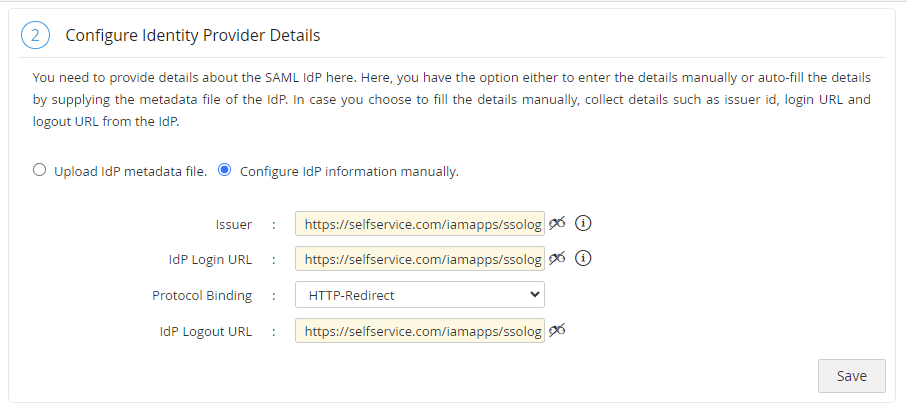
- In the Configure Identity Provider Details section, you can either choose the Upload IdP metadata file option or the Configure IdP information manually option.
- If you choose the Upload IdP metadata file option, upload the metadata file downloaded in step 5a of the prerequisites and click Upload.
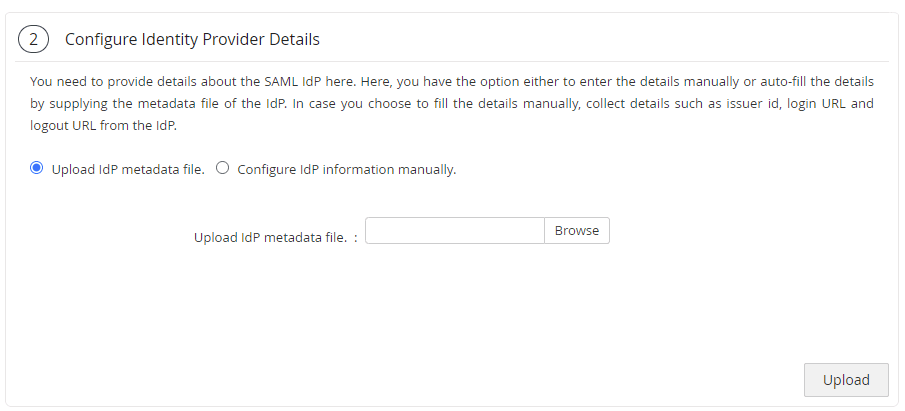
- If you choose the Configure IdP information manually option, paste the Entity ID value copied in step 5b of the Prerequisites in the Issuer field.
- In the IdP Login URL field, enter the Login URL value copied in step 5b of the Prerequisites.
- Choose the HTTP-Redirect binding option in the Protocol Binding field.
- In the IdP Logout URL field, enter the Logout URL value copied in step 5b of the Prerequisites.
Note: The Logout URL is optional and can be skipped if single logout (automatically log out from ADSelfService Plus when logging out from Access Manager Plus) is not required.
- Click Save.
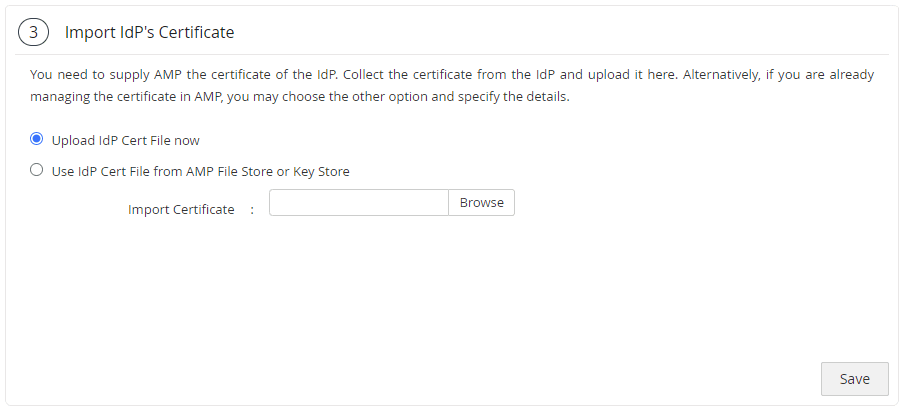
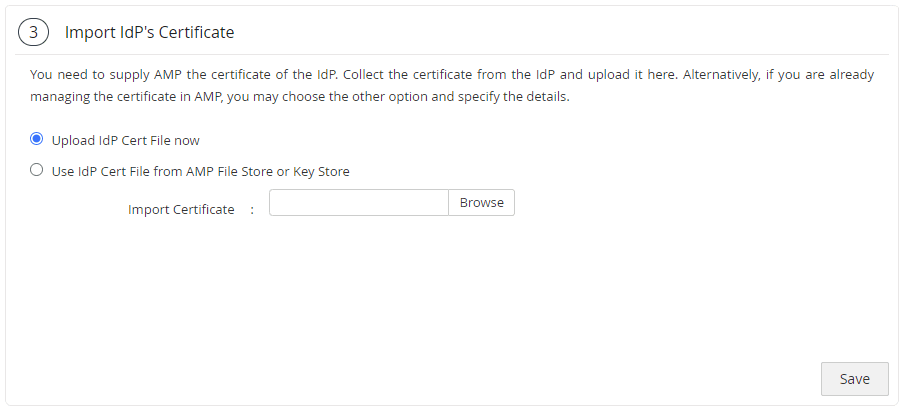
- In the Import IdP's Certificate section, select the Upload IdP Cert File now option.
- In the Import Certificate field, upload the X.509 certificate downloaded in step 5b of the Prerequisites and click Save.
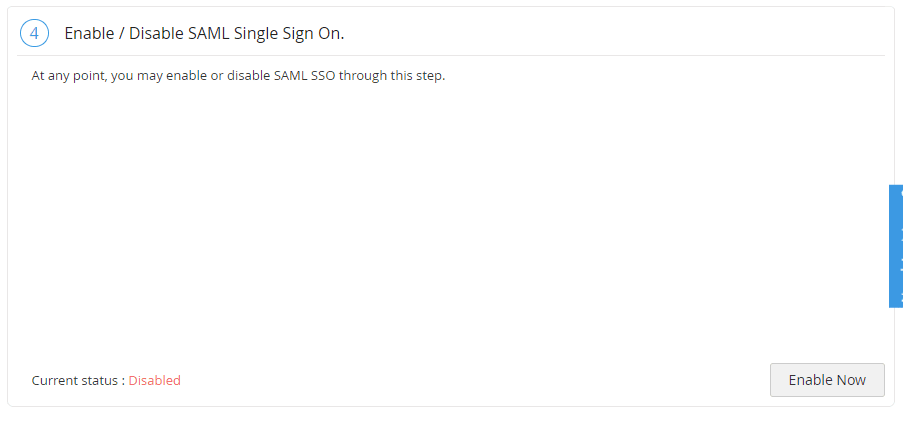
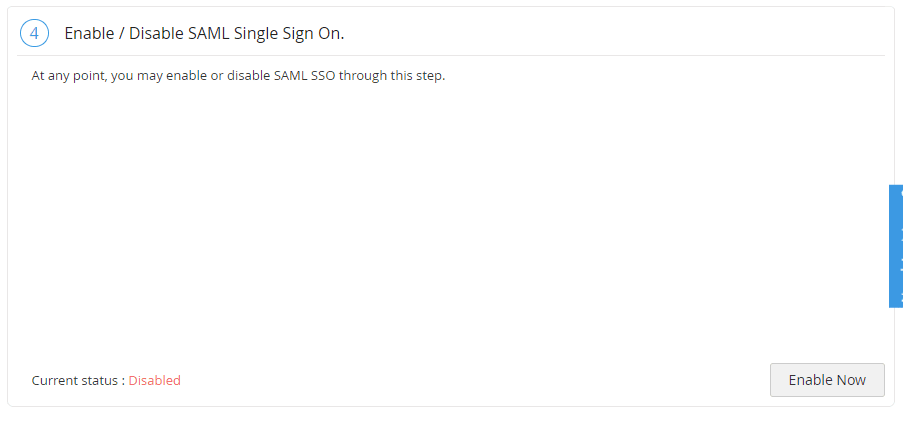
- In the Enable/Disable SAML Single Sign On section, click the Enable Now button.
ADSelfService Plus (identity provider) configuration steps
- Switch to ADSelfService Plus' Access Manager Plus configuration page.
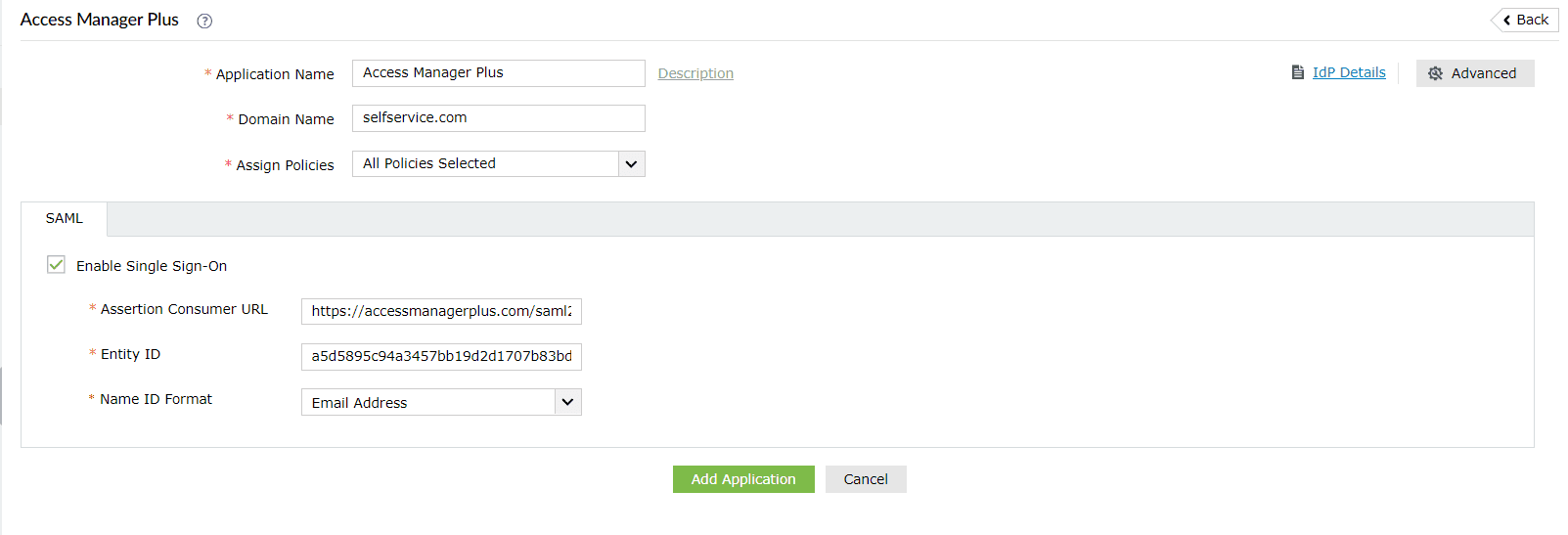
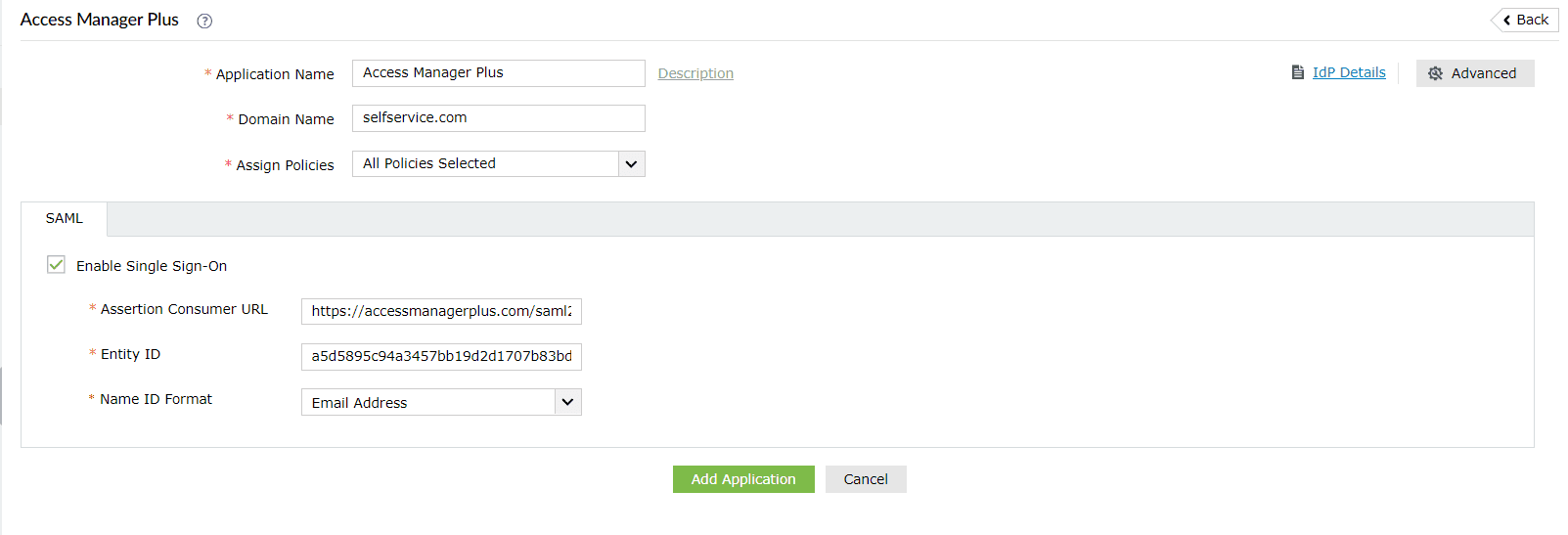
- Enter the Application Name and Description.
- Enter the Domain Name of your Access Manager Plus account. For example, if you use johndoe@pmp.com to log in to Access Manager Plus, then amp.com is the domain name.
- In the Assign Policies field, select the policies for which SSO needs to be enabled.
Note: ADSelfService Plus allows you to create OU- and group-based policies for your AD domains. To create a policy, go to Configuration > Self-Service > Policy Configuration > Add New Policy.
- Select the SAML tab and check Enable Single Sign-On.
- In the Assertion Consumer URL field, enter the Assertion Consumer URL copied in step 3 of Access Manager Plus configuration.
- In the Entity ID field, enter the Entity Id value copied in step 3 of Access Manager Plus configuration.
- In the Name ID Format field, choose the format for the user login attribute value specific to the application.
Note: Use Unspecified as the default option if you are unsure about the format of the login attribute value used by the application.
- Click Add Application.
Your users should now be able to sign in to Access Manager Plus through the ADSelfService Plus portal.
Note: For Access Manager Plus, both service-provider-initiated and identity-provider-initiated flows are supported.