Configuring SAML SSO for ScreenSteps
These steps will guide you through setting up the single sign-on functionality between ADSelfService Plus and ScreenSteps
Prerequisite
-
Log in to ADSelfService Plus as an administrator.
- Navigate to Configuration → Self-Service → Password Sync/Single Sign On → Add Application, and select ScreenSteps from the applications displayed.
Note: You can also find ScreenSteps application that you need from the search bar located in the left pane or the alphabet wise navigation option in the right pane.
-
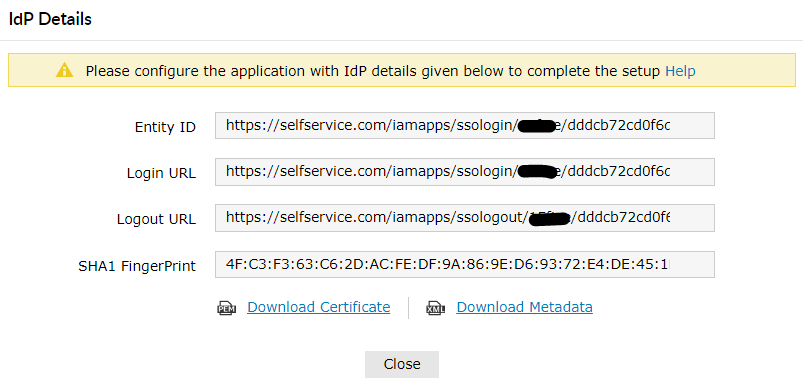
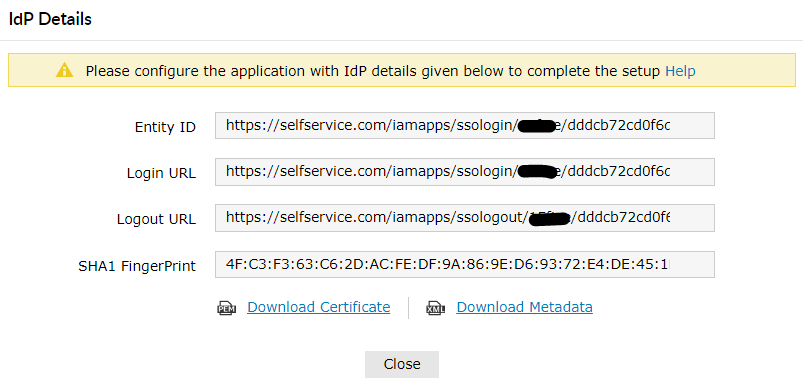
Click IdP details in the top-right corner of the screen.
-
In the pop-up screen that appears, note down the values of Login URL , Logout URL and download the sso ceritificate by clicking Download Certificate.
ScreenSteps (Service Provider) configuration steps
-
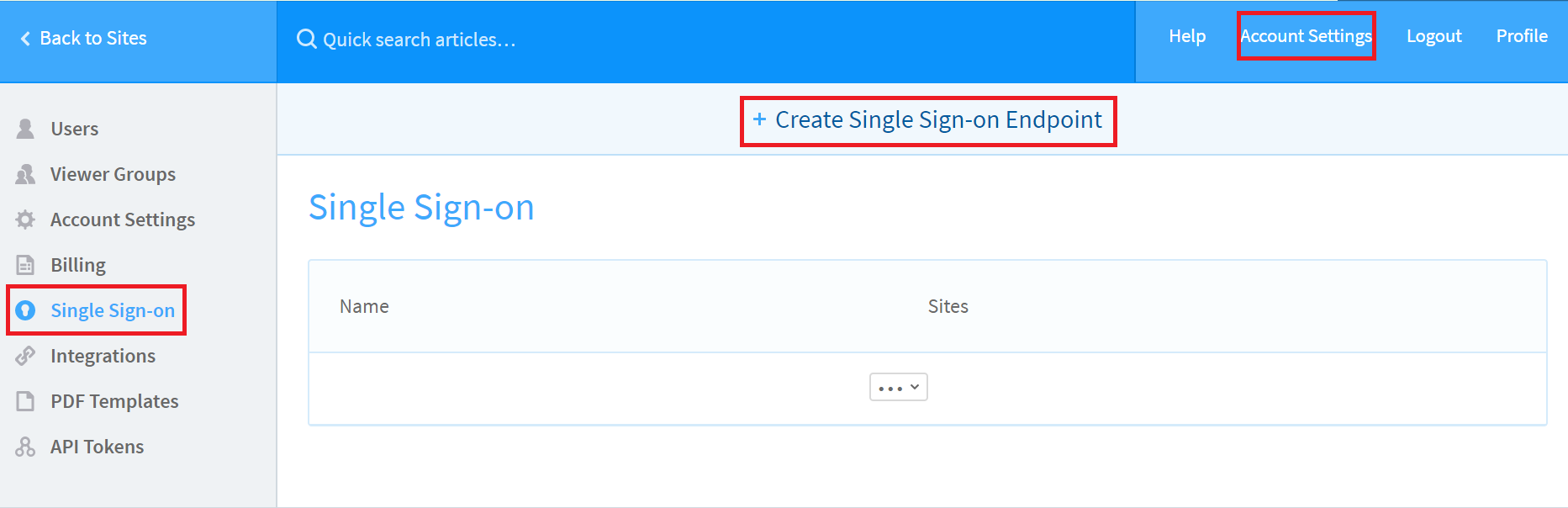
Now, log in to your ScreenSteps administrator account.
-
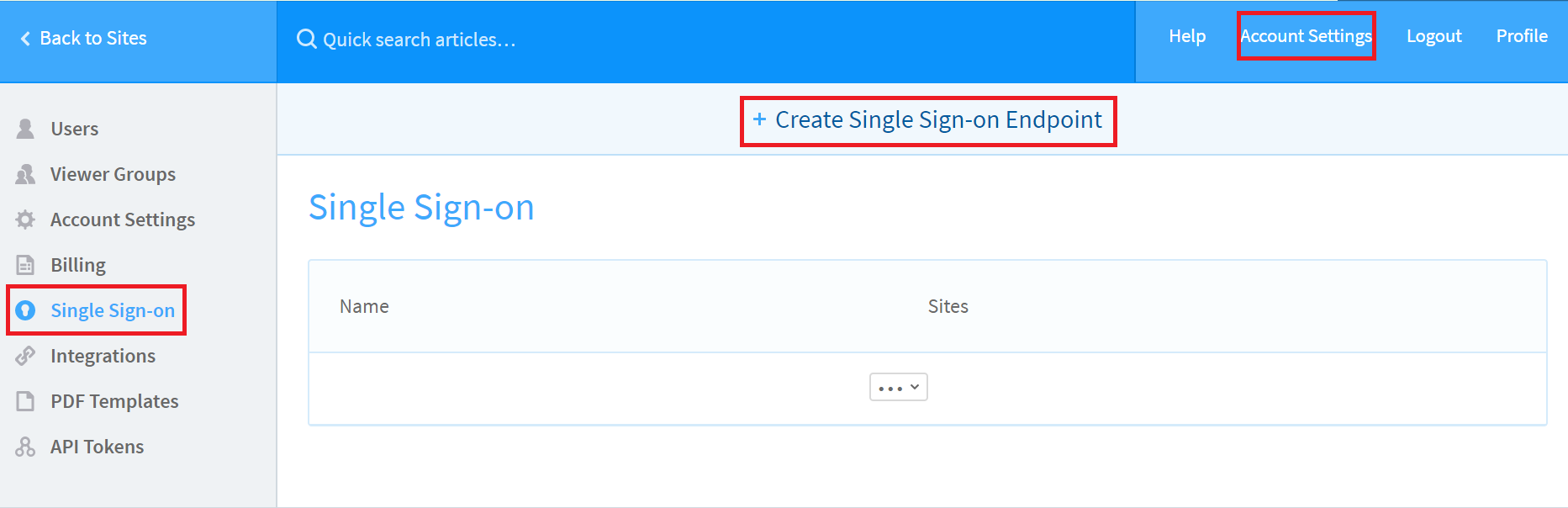
In the left pane, click Single Sign-on.
-
Click Create Single Sign-on Endpoint
-
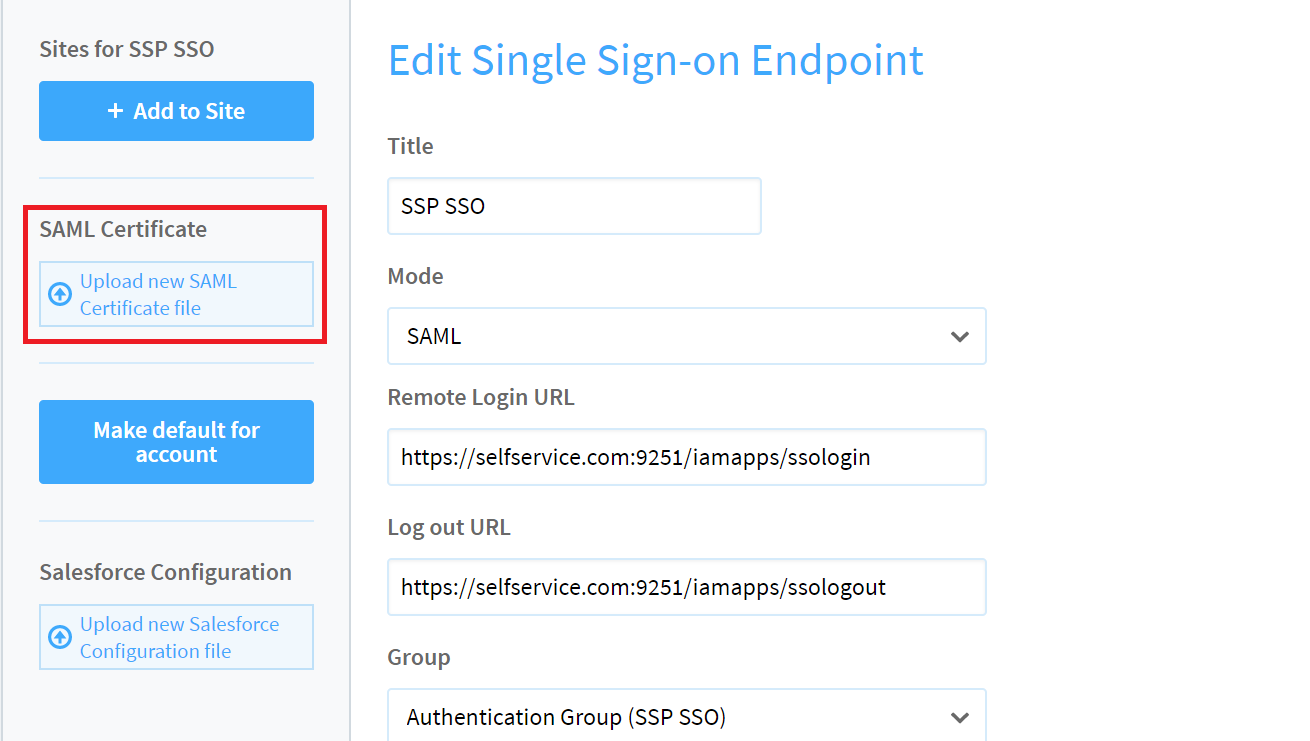
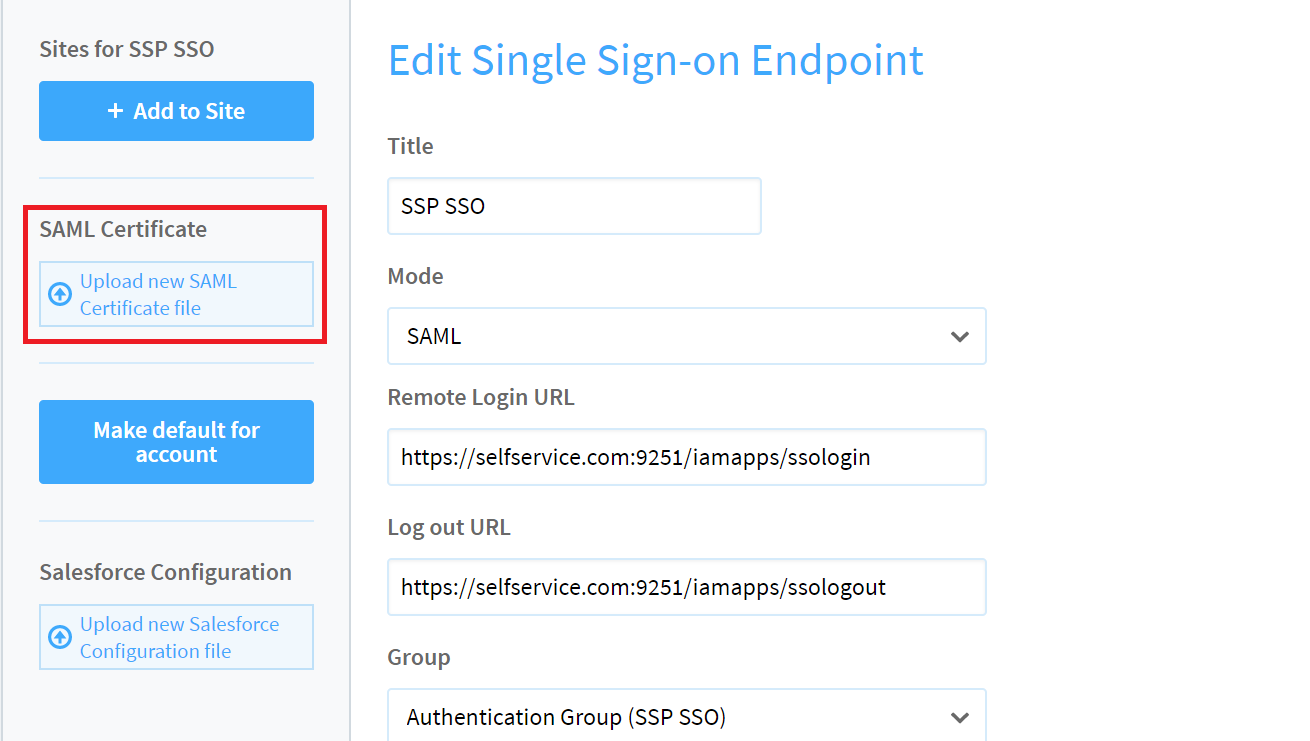
Enter a ScreenSteps of your choice and set the Mode to SAML.
-
In the Remote Login URL field, enter the Login URL value that you had saved in Step 4 of Prerequisite.
-
In the Log out URL field, enter the Logout URL value that you had saved in Step 4 of Prerequisite.
-
Click Create.
-
In the middle pane, click Upload new SAML Certificate file. Select the PEM certificate file you had saved in Step 4 of Prerequisite.
-
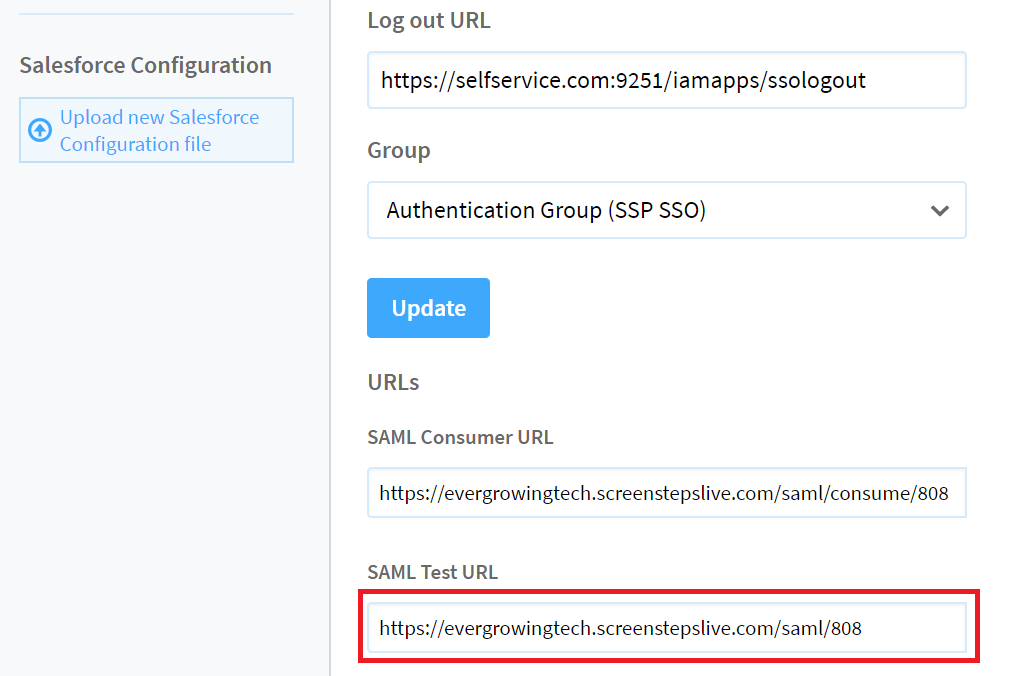
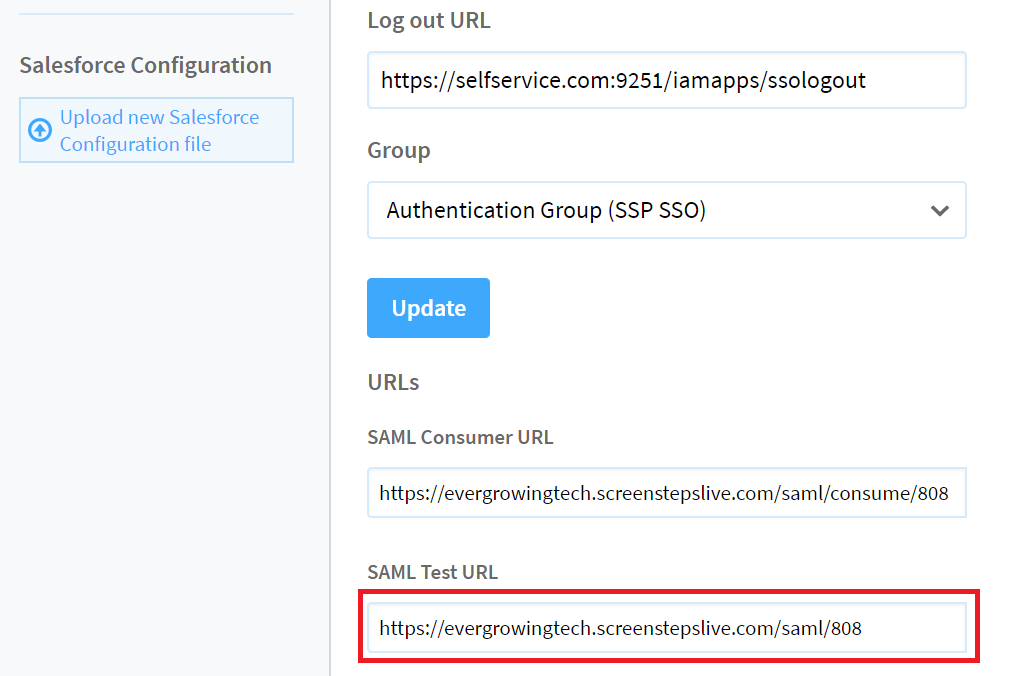
Click Update.
-
Note down the value in SAML Test URL field.
ADSelfService Plus (Identity Provider) configuration steps
-
Now, switch to ADSelfService Plus’ ScreenSteps configuration page.
-
Enter the Application Name and Description.
-
In the Assign Policies field, select the policies for which SSO need to be enabled.
Note:ADSelfService Plus allows you to create OU and group-based policies for your AD domains. To create a policy, go to Configuration → Self-Service → Policy Configuration → Add New Policy.
-
Select Enable Single Sign-On.
-
Enter the Domain Name of your ScreenSteps account. For example, if you use johndoe@thinktodaytech.com to log in to ScreenSteps, then thinktodaytech.com is the domain name.
-
In the SAML Redirect URL field, enter the value you had saved in Step 10 of ScreenSteps configuration.
-
Enter the Assertion Consumer Service URL provided by your application service provider in the Assertion Consumer Service URL field. If required, click the + button next to the text field to add multiple Assertion Consumer URLs. These values can be found in the application's SSO configuration page or metadata. Please reach out to your application's support team if you are having trouble locating the Assertion Consumer Service URL in your application's user interface or metadata.
-
In the Name ID Format field, choose the format for the user login attribute value specific to the application.
Note: Use Unspecified as the default option if you are unsure about the format of the login attribute value used by the application.
-
Click Add Application
Your users should now be able to sign in to ScreenSteps through ADSelfService Plus.
Note:
For ScreenSteps, only IdP-initiated flow is supported.